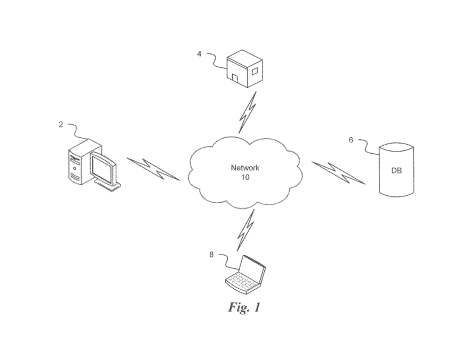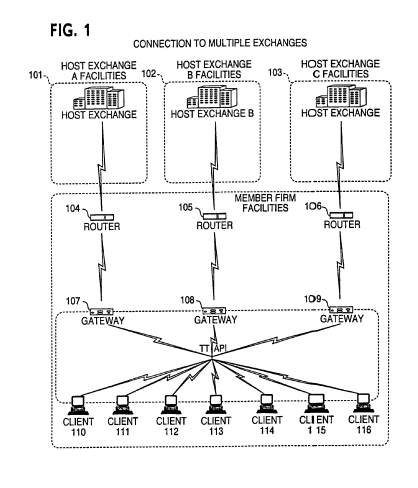
Automated Alerts
A system for handling and managing critical incidents. System has a mapping module configured to receive alert
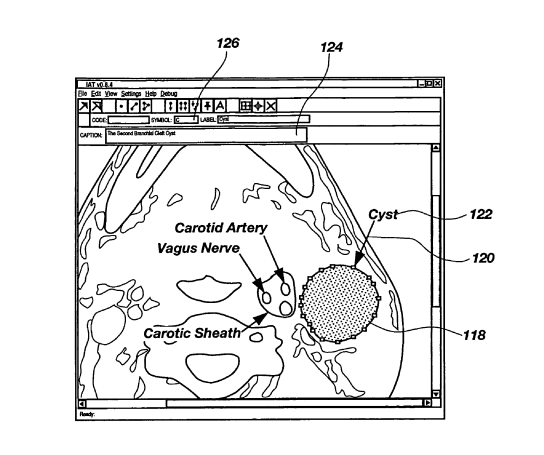
Artificial Human
AI-powered virtual being looks and behaves like human beings. Virtual being converse and sympathies
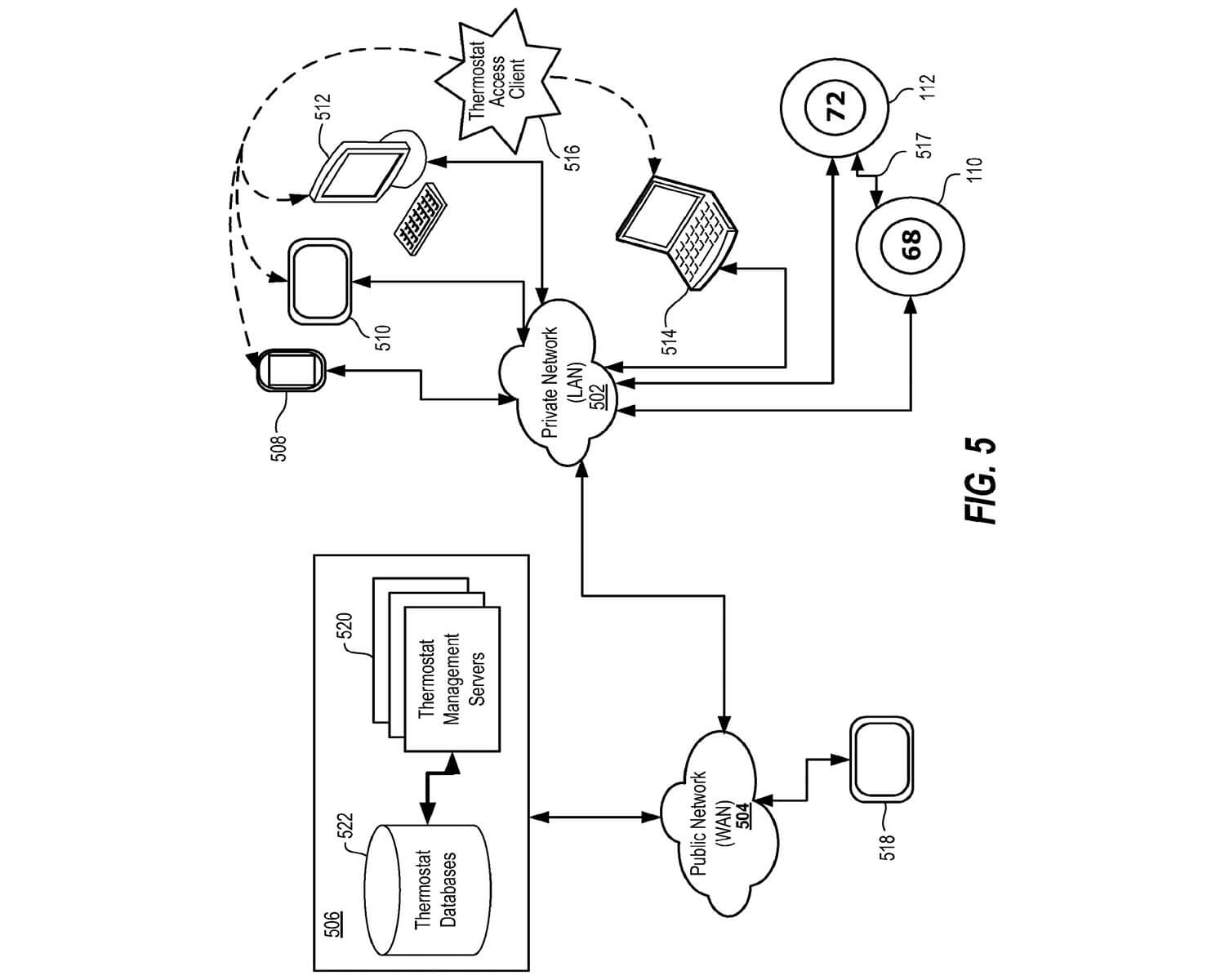
AI (Data Cleaning)
The focus of this study is to investigate novel process and methods for managing databases,